In this post I describe how you can add a CentOS 7 host to a Windows Active Directory domain. Happy experimenting.
Precondition:
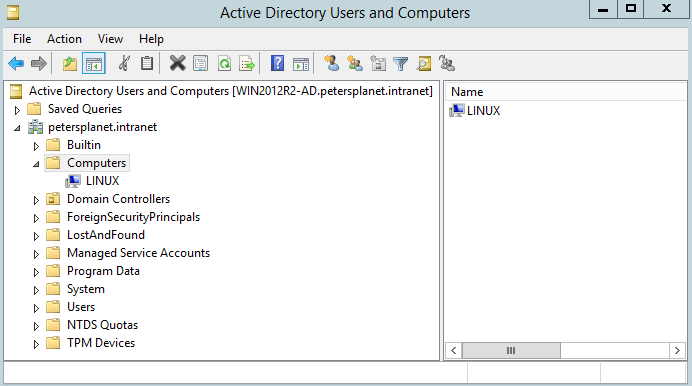
Windows 2012R2 with Windows Active Directory services in place.
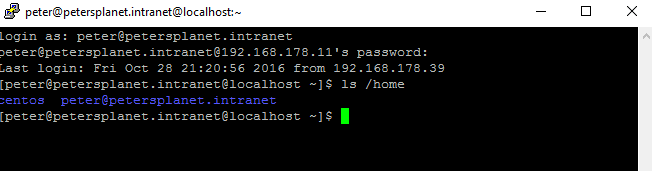
A Linux server. In this case CentOS 7.
On Windows
Add the Linux server in DNS for the forward lookup zone including the associated pointer record.
Make sure you have a user with sufficient priviliges to add a server to a domain.
On Linux
Install the necessary additional packages.
Make sure the Linux server uses the DNS server of the Windows domain.
yum -y install sssd realmd krb5-workstation
Create an empty sssd.conf
cp /usr/share/doc/sssd-common-1.13.0/sssd-example.conf /etc/sssd/sssd.conf chmod 600 /etc/sssd/sssd.conf
The Linux server is not part of a domain.
Some checks:
realm discover realm discover petersplanet.intranet
Now it is time to add the Linux server to the Windows domain:
realm join -U peter@petersplanet.intranet petersplanet.intranet realm discover petersplanet.intranet
Test the result:
getent passwd peter@petersplanet.intranet
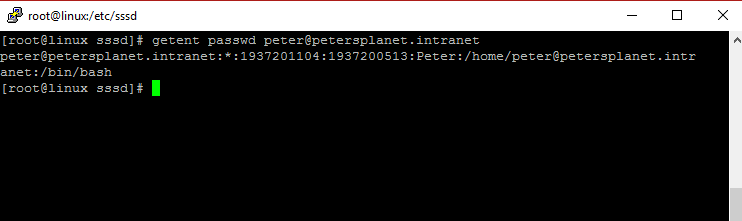
A disadvantage is that it looks like you always have to use the fully qualified domain name (FQDN) for a user.
Now it is time to finetune the configuration. For instance limit the acces to the Linux host for a certain group of users.
The contents of /etc/sssd/sssd.conf which has been generated by the realm command can be seen below:
[sssd] config_file_version = 2 services = nss, pam domains = petersplanet.intranet [nss] [pam] [domain/petersplanet.intranet] ad_domain = petersplanet.intranet krb5_realm = PETERSPLANET.INTRANET realmd_tags = manages-system joined-with-samba cache_credentials = True id_provider = ad krb5_store_password_if_offline = True default_shell = /bin/bash ldap_id_mapping = True use_fully_qualified_names = True fallback_homedir = /home/%u@%d access_provider = ad
References:
https://fedorahosted.org/sssd/wiki/Configuring_sssd_with_ad_server
http://docs.aws.amazon.com/directoryservice/latest/admin-guide/join_linux_instance.html